Unveiling the Hidden Dangers of Cloud-Based Encryption: How Microsoft’s BitLocker Policy Puts Your Data at Risk
Unveiling the Hidden Dangers of Cloud-Based Encryption: How Microsoft’s BitLocker Policy Puts Your Data at Risk
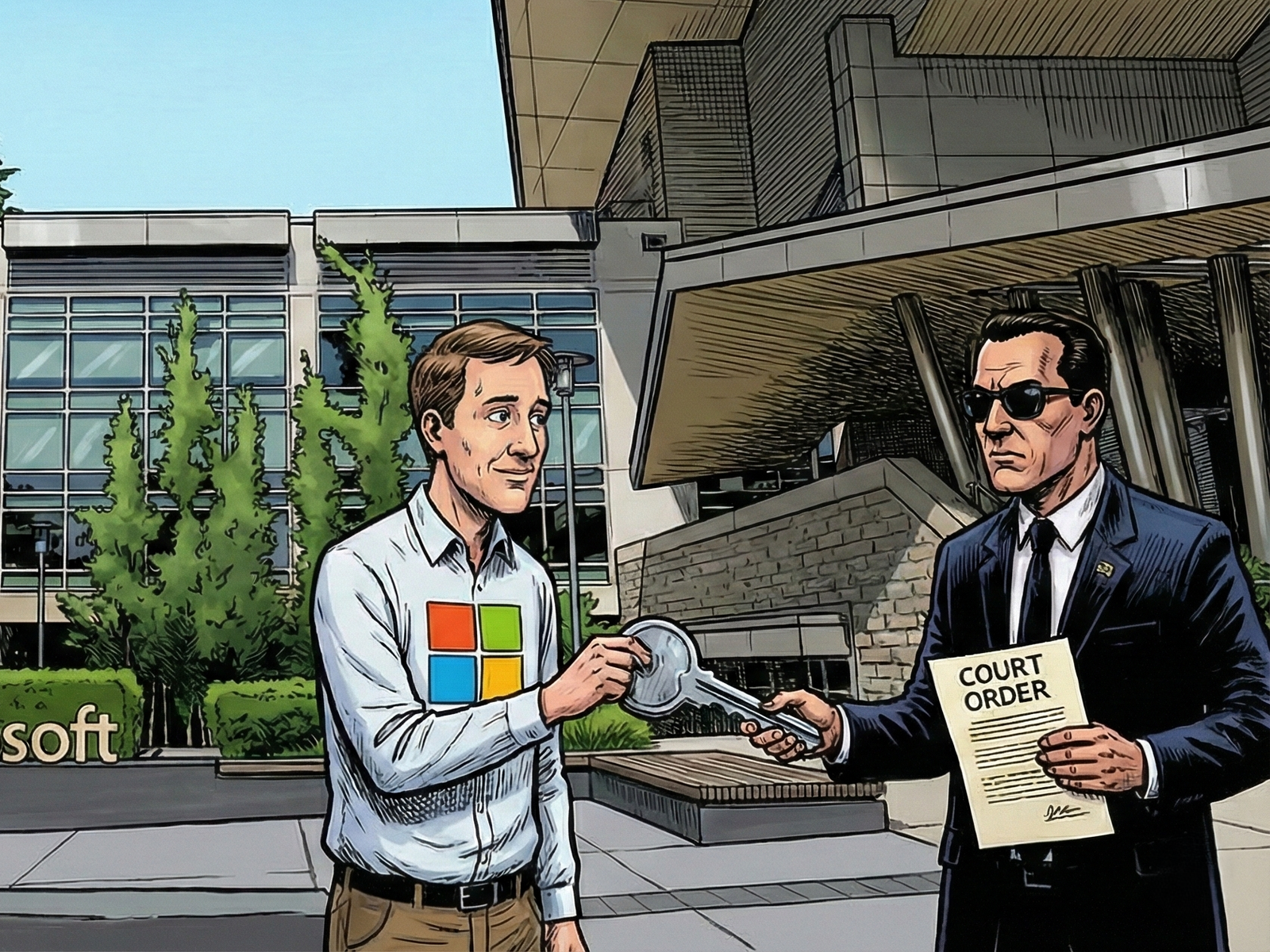
When it comes to data security, encryption is a vital aspect of protecting sensitive information. However, a recent revelation has cast a shadow over Microsoft’s BitLocker encryption, a widely-used security feature in Windows. It appears that Microsoft occasionally hands over BitLocker keys to law enforcement agencies, such as the FBI, upon request.
This may come as a surprise to many, especially when compared to the stance taken by other tech giants like Apple and Google. These companies have consistently maintained that they cannot unlock customer devices, even when faced with requests from law enforcement. The situation with Windows encryption, however, paints a different picture.
The main concern here is the potential risk associated with storing BitLocker keys in the cloud. While Microsoft’s intention behind this move might be to provide a convenient backup solution for users, it inadvertently creates a vulnerability that can be exploited by authorities. This raises questions about the true extent of data security and the boundaries of cooperation between tech companies and law enforcement.
As the use of cloud-based services continues to grow, it is essential to analyse the implications of such policies on our data. The fact that Microsoft can access and share BitLocker keys with law enforcement agencies undermines the very purpose of encryption, which is to ensure the confidentiality and integrity of data.
In light of this, it is crucial for individuals and organisations to reassess their approach to data security. By understanding the potential risks associated with cloud-based encryption, we can take proactive measures to protect our sensitive information. This may involve exploring alternative encryption methods or adopting a more cautious approach to storing data in the cloud.
Ultimately, the onus lies with tech companies to be transparent about their data handling practices and ensure that adequate safeguards are in place to prevent unauthorised access. As we navigate the complex landscape of cloud security, it is vital to strike a balance between convenience and data protection, without compromising on the fundamental principles of confidentiality and privacy.






